While the average cost of a data breach will exceed $9 million by 2021, the calculation for cyber-physical attacks prevalent in the healthcare industry is still uncertain and unpredictable. The US government is shedding new light on the growing problem of global cyber conflict and threat actors.
Despite the rise of ransomware, many stakeholders in the industry remain in the dark when it comes to understanding the cyber-physical threats associated with operational medical technology, the Internet of Medical Things (IoMT), and the digital components of operations and facilities management.
From business records to patient information and diagnostics, scheduling, treatment, prescriptions, payments, utilities and more, medical care has digitized, medical technologies, devices, hospitals and public health facilities have one theme cutting across the cyber threat landscape: confusion.
Often introduced without security policy alignment, the push to condense multiple connected endpoints into a “single pane of glass” makes technologies that are easy to deploy but difficult to secure. Like a house of mirrors, responsibility for understanding and mitigating cyber risk in healthcare is difficult to define and often depends on who you ask, especially when it comes to systems and devices outside of an organization.
The IoMT represents a two-way mirror that provides a window into targeting med-tech and healthcare networks and activities. Hardcoded passwords and credentials have been targeted, user interfaces have been hacked from manufacturers, management processes have been compromised, and widespread vulnerabilities continue to affect thousands of devices around the world.
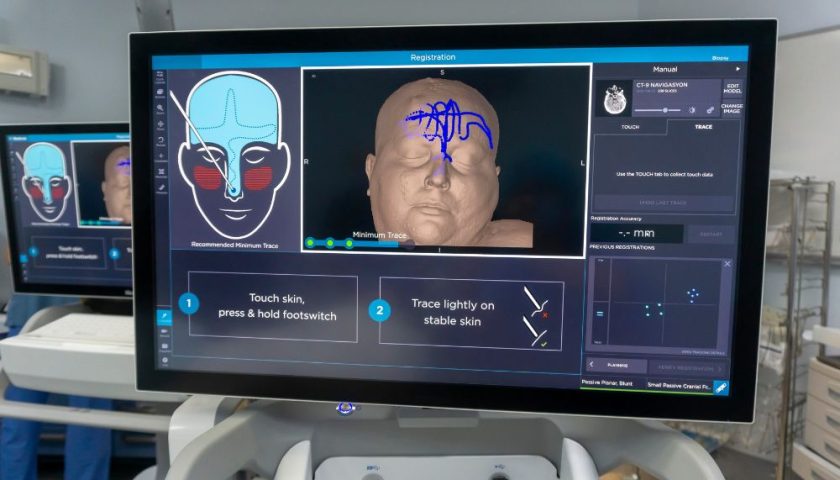
Surgical technology, IoMT technologies and facility systems consist of a variety of machines and structures to include anesthesia machines and bedside monitors, medical imaging equipment, insulin pumps, fluid pumps, ventilators and a growing list. Sensors, cameras, wearables and analytics that activate or report the status of devices, processes and operations.
Cybersecurity threats to healthcare are multifaceted, including vulnerable technologies designed without security in mind, Internet-connected devices used directly in patient care, and technology in smart buildings and automated facilities.
According to the FDA, “failure to maintain cybersecurity throughout the medical device product lifecycle can result in compromised functionality, loss of medical or personal information, inadequate data integrity, or the spread of security threats to other connected devices or networks… Harm to the patient such as illness, injury or death due to treatment delays or other effects on the availability and function of medical equipment.
Old medical technology
Legacy technologies in healthcare are ubiquitous, expensive to replace, and vulnerable to exploitation by popular cyberattack tactics and publicly disclosed common vulnerabilities and vulnerabilities (CVEs). Many of them work with outdated software, such as Windows XP and Windows 7, and have mechanisms for applying critical updates and upgrades to widely distributed and unmanaged deployments. Resources and manpower limit the ability to track, maintain, and continuously enhance every element of advanced medical technology currently in use.
At the highest level, manufacturers are responsible for product security, lifecycle maintenance, vulnerability disclosure, and creating and distributing available fixes and updates for the continuously secure devices and technologies they manufacture.
End users, at the same time, are responsible for monitoring and resolving discovered vulnerabilities, enabling security features, protecting data in transit and at rest, and deploying solutions to monitor technologies and networks operating within their organization. At the same time, most groups and places are not ready to return to manual labor for any length of time.
Internet of Medical Devices (IoMT)
According to the Food and Drug Administration, the United States regulates approximately 200,000 medical devices manufactured by more than 18,000 companies worldwide. Smart, connected medical devices include both user interfaces (for patients and healthcare providers) as well as machine-to-machine communications via network connectivity.
These devices, which are often connected to the Internet, have risks related to unauthorized access, hacking of login interfaces, bypassing password authentication, denial of service (DDoS) attacks, and sensitive patient data protections.
The main attack surface for IoMT devices is default credentials over SSH. When a system is targeted, the attacker, typically another infected IoT device, will try an average of forty passwords for a few usernames. Other common attack points for these devices include UPnP, HTTPS, and the underlying Java packages and various source code modifications.
As most IoT devices are headless (no user interface) and are not designed for automatic updates if the end user does not agree to a risk-based specification, these systems and variants remain unpatched long after a patch is released. – User license agreements.
Smart, connected appliances
Medical and healthcare operations and utilities continue to digitize parts of non-IT control systems – fire alarm and prevention, electrical and lighting systems, metering systems, vehicle charging stations, key access controls. As controls become centralized, companies often deploy building automation solutions (BAS) to connect and automate these various functions. Security flaws in BAS can target credentials, networks, and VPNs to access sensitive information.
In a recent Smart Building engagement, we found 361 insecure protocols in use, 259 open device vulnerabilities, and 37 plaintext (unencrypted) passwords in use.
When controlling one or more devices, threat actors can coordinate more widespread attacks depending on the level of communication.
Cyber security is critical to operations and facilities in the hospital where critical personnel gather, and secure movement of resources, equipment, and personnel is essential. Remote and privatized operations may struggle to find and maintain cybersecurity resources.
Major companies and providers struggle to manage massive campuses, some the size of small cities, serving millions of patients each year and employing tens of thousands of people. Building, facility, and security control systems can have a significant impact on patient care and patient and provider safety. Before the U.S. National Cyber Directorate prioritizes, comprehensive security practitioners must chart the course.
The way forward
If legacy med-tech, IOMT equipment, and facilities technology are not targeted in a cyber incident, the effects of an outage can render them useless, delaying treatment and harming patients and providers. When enterprise IT systems fail, they are often isolated from the rest of the network. When operating systems fail, the effects can be property and damage.
This modus operandi creates a distinction between risk management frameworks and incident reporting. Central security problems continue to arise. This situation begs the question: Do IT and facilities teams know what else is connected to communication networks and the potential use of these legacy systems, IoMT devices, networks and control systems?
Faced with an over-reliance on technology and burdens of manual tasks, hospitals and healthcare providers are reducing cybersecurity risks, complying with rapidly changing regulatory requirements, and working to gain visibility into communications, traffic and abnormalities related to their network behavior.
With the magnitude of potential risks, transparency is key. A cybersecurity solution designed for operational technology and IOMT can:
- Capture and visualize tens or hundreds of thousands of connected systems and endpoints
- Monitor and monitor network traffic in real time to include non-IT systems
- Understand the basics and the state of your organization’s cyber security on an ongoing basis
- Provide actionable intelligence to solve critical issues
- Restrict third-party access and provide alerts on changes to network properties or variables
- Strengthening the organization’s security policy without gaps or shadow-connections
Photo: Traitov, Getty Images